TOTAL ISPs
3439
-
From Yemen 2 hours ago
-
From India 17 hours ago
-
From Nepal 2 days ago
-
From Mauritius 2 days ago
-
From Pakistan 3 days ago
-

-

Bring back the full row green color
Please yes can you give us a choise geen bubles or green lines. I missed a client recently when he was oof and i did not see the entire row just a portion of it, and it was just white.9 days ago by Saint Patrick -

Bring back the full row green color
Could you please bring back the full row green color? I see some nice updates, but the full colored row was a good one. Why did you removed??21 days ago by MAG -

Walled Garden for blocked user
A captive portal for notification will be great. Thank you. and keep up the good work!2 months ago by Manat -

Whatsapp api option for notifying custoimer
I’ve been using [ultramsg](https://ultramsg.com) lately for WhatsApp automation, and it made sending alerts and handling support chats way smoother. Setup was quick with the QR login, and I liked that it worked with the scripts I already had in Python. The pricing felt fair for what I needed, especially with webhooks and media messages baked in.2 months ago by Mike -

API / webhook for Accounting software integration
yes i try but it was only to fetch the expired customer i want the api to renew the plan.2 months ago by Vikram -

Custom domain of zima
You can do this in the Custom domain section in Zima. You go to My account, Custom Domain. It has a wizard that will guide you and gives you the instructions to setup your custom domain.2 months ago by Support -

Configuration of different dns for multiple ip adress
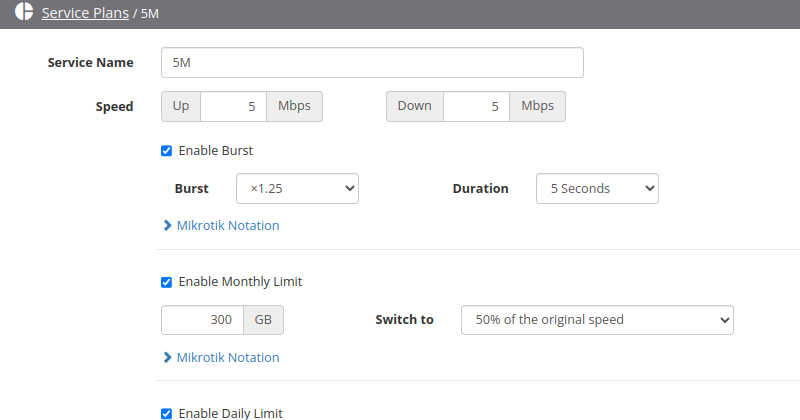
in service plan section, under IP pool, we could add a section for DNS. If not specified it defaults to the main DNS. Otherwise it sets the DNS that you specify there. Will this answer your use case?2 months ago by Support -

Walled Garden for blocked user
Walled garden concept exists with Hotspot protocol. With PPP it is impossible to do redirect page. We have a plan to work on captive portal with DHCP protocol. It could be the closest solution to your requirement. Another method that could work also is the notifications feature: sending email or sms or whatsapp to user to notify. Which method do you prefer?2 months ago by Support -

API / webhook for Accounting software integration
Did you try Zima API? You can go to Zima, My account, and check the APi section there. There you can generate API key and use the existing functions. Let me know once youndo and I will assist you further.2 months ago by Support